WASHINGTON (AP) — Pro-Iranian hackers are targeting sites in the Middle East and starting to stretch into the United States during the war, raising the risk of American defense contractors, power stations and water plants being swept into a wave of digital chaos that could expand if Tehran's allies join the fray.
Hackers supporting Iran claimed responsibility for a significant cyberattack Wednesday against U.S. medical device company Stryker. Since the war began Feb. 28, they also have tried to penetrate cameras in Middle Eastern countries to improve Iran's missile targeting. They have targeted data centers in the region, as well as industrial facilities in Israel, a school in Saudi Arabia and an airport in Kuwait.
Click to Gallery
A woman gathers belongings from her family's home after it was damaged by a projectile launched from Lebanon, in Haniel, central Israel, Thursday, March 12, 2026. (AP Photo/Baz Ratner)
FILE - Stryker CEO Kevin Lobo is seen at a groundbreaking ceremony for their building in Portage, Mich., July 24, 2017. (Mark Bugnaski/Kalamazoo Gazette-MLive Media Group via AP, File)
FILE - Rescue workers and residents search through the rubble in the aftermath of a strike on a girls' elementary school in Minab, Iran, Feb. 28, 2026. (Abbas Zakeri/Mehr News Agency via AP, file)
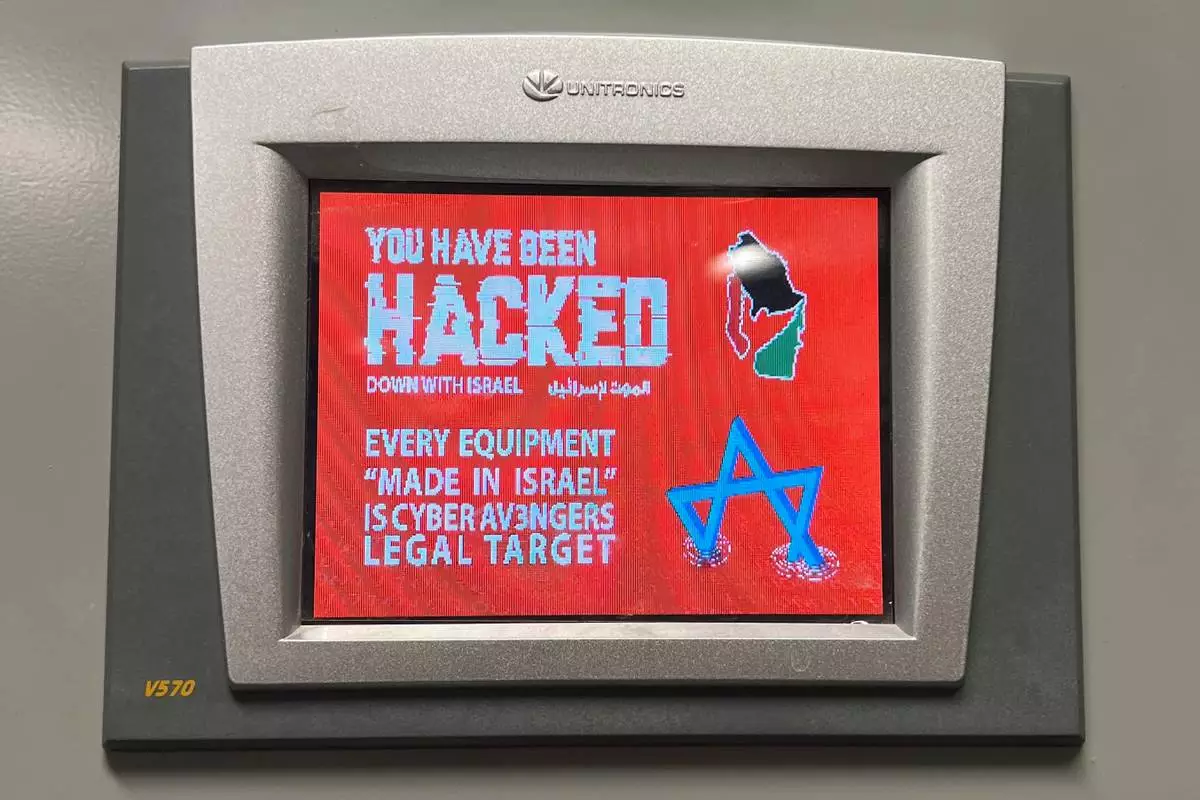
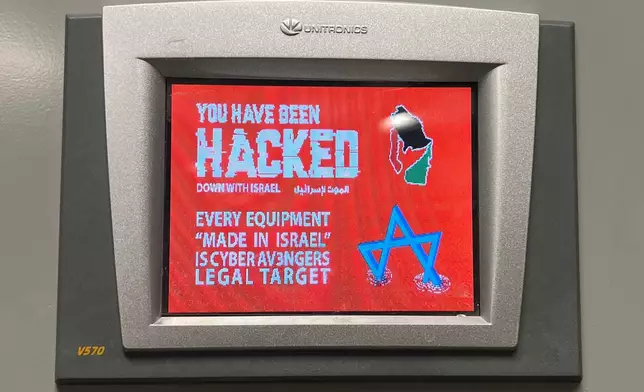
FILE - This photo provided by the Municipal Water Authority of Aliquippa shows the screen of a Unitronics device that was hacked in Aliquippa, Pa., Nov. 25, 2023. (Municipal Water Authority of Aliquippa via AP, File)
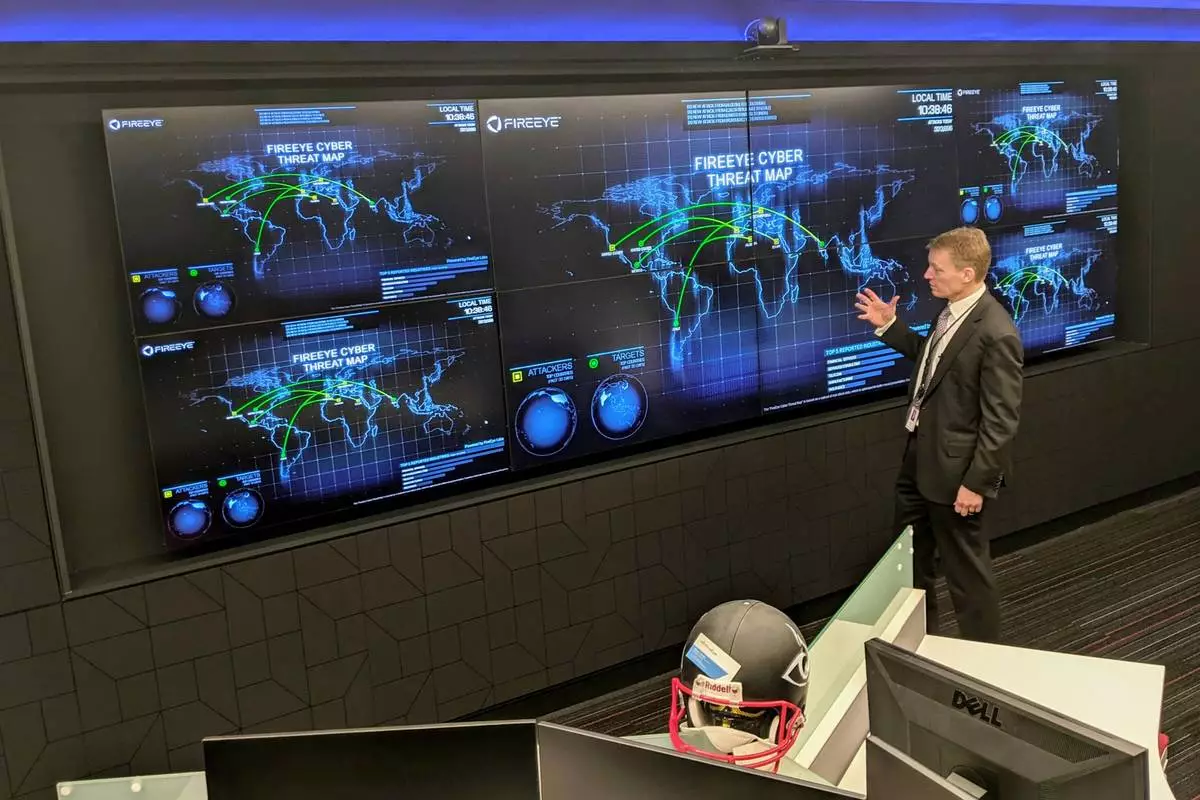
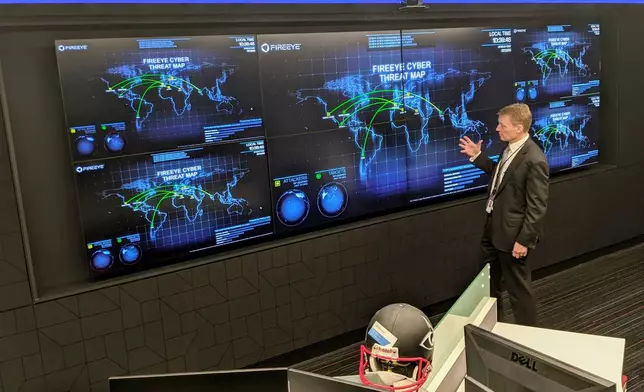
FILE - The CEO of FireEye Kevin Mandia gives a tour of the cybersecurity company's unused office space in Reston, Va., March 9, 2021. (AP Photo/Nathan Ellgren, file)
Iran has invested heavily in its offensive cyber capabilities while cultivating ties to hacking groups. In recent years, groups working for Tehran have infiltrated the email system of President Donald Trump's campaign, targeted U.S. water plants and tried to breach the networks used by the military and defense contractors.
The goal is to wear down the American war effort, drive up the costs of energy, strain cyber resources and cause as much pain as possible for American companies that depend on the defense industry.
“Something is going to happen because the gloves are off," said Kevin Mandia, founder of the cybersecurity companies Mandiant and Armadin.
Pro-Iranian, pro-Palestinian hackers claimed credit for disrupting systems at Stryker, a Michigan-based medical technology company. A group known as Handala said the attack was in retaliation for suspected U.S. strikes that killed Iranian schoolchildren.
Like other ideologically motivated hackers, profit is not Handala’s goal, according to Ismael Valenzuela, vice president of threat intelligence at the cybersecurity company Arctic Wolf.
“What distinguishes this group is its clear focus on data destruction rather than financial extortion,” he said in an email.
Polish authorities are investigating a recent cyberattack — on a nuclear research facility — that may have ties to Iran, though they acknowledge that another group could be behind the attack and using the Iran war to mask its identity.
Going forward, U.S. defense contractors, government vendors and businesses that work with Israel are likely targets, as is critical infrastructure such as hospitals, ports, water plants, power stations and railways.
Pro-Iranian hackers openly discuss their plans in Telegram and other online message boards.
“The datacenters need to be taken out,” wrote one user, as uncovered by researchers at U.S.-based SITE Intelligence Group. “They host the brains of USAs military communication and targeting systems.”
Cyber operations also gather intelligence — for example, Iran's effort to hack into cameras in neighboring countries to aid its missile targeting. Infiltrating U.S. networks, meanwhile, would offer view into military planning or supply chains.
The strikes on Iran's military as well as internet outages may have limited Iran's cyberattacks in the short term. But experts say Iranian hackers and their allies will aim for quick victories by targeting the weakest links in American cybersecurity.
Often, local water plants or health care facilities lack the funds and know-how to install the latest software patches or take other security steps. That has made them a favorite target, both because of the relative ease of penetrating them and because of the panic these disruptions can cause.
This can include denial-of-service attacks, in which hackers try to jam a network so legitimate users cannot use it, and website defacements, which can prevent a company from communicating with customers. Hack-and-leak operations, where hackers threaten to release sensitive stolen material, are another possibility.
The attacks are not that sophisticated, according to Shaun Williams, a former FBI and CIA officer who is now a senior director at the cybersecurity firm SentinelOne. But if a business or government agency has failed to keep up with its cybersecurity, it could pay a steep price, he said.
“Patch your systems. Ensure your firewalls and security solutions are up to date,” Williams said. “Remove your stale accounts. All the cyber hygiene that you should be doing, it’s more critical now than ever. Prepare for disruption.”
Russia and China present the greatest cyber threats to the U.S., while North Korea is a growing concern. But what Iran has lacked in resources it has made up for in ingenuity, experts say.
In recent years, Tehran's digital warriors have impersonated American activists online to covertly encourage protests against Israel on college campuses. They have set up fake news websites and social media accounts primed to spread false and exaggerated claims before big U.S. elections.
In 2024, Iranian hackers infiltrated the email system of the Trump campaign and later tried to disseminate files that the hackers said they stole. Hackers linked to Iran also tried to hack into the WhatsApp accounts of both Trump and his then-Democratic opponent, President Joe Biden.
The activity prompted the Department of Homeland Security to issue a public warning last year about Iranian cyber threats.
“Iran and especially the proxies don’t care how big or smart you are. This is about making an impact, about creating chaos,” said James Turgal, a cybersecurity expert who spent 22 years as an FBI agent and is now a vice president at Optiv, a Denver-based information security firm.
Experts are watching closely to see if Russia, China or hacking groups allied with either country provide hacking assistance to Iran, mounting attacks intended to undermine American operations in Iran and make it harder for the U.S. to sustain its fight.
While China has so far taken a cautious approach, there is evidence that pro-Iranian hackers in Russia are already at work. Researchers at the cybersecurity firm CrowdStrike detected a surge of activity from Russian hackers in support of Tehran since the war began.
One group known as Z-Pentest claimed responsibility for disrupting several U.S. networks, including some involved in closed-circuit video cameras.
The timing of the attack suggests the hackers were targeting U.S. interests because of the war in Iran, according to Adam Meyers, head of counter adversary operations at CrowdStrike.
“Western organizations should continue to remain on high-alert,” Meyers said.

A woman gathers belongings from her family's home after it was damaged by a projectile launched from Lebanon, in Haniel, central Israel, Thursday, March 12, 2026. (AP Photo/Baz Ratner)

FILE - Stryker CEO Kevin Lobo is seen at a groundbreaking ceremony for their building in Portage, Mich., July 24, 2017. (Mark Bugnaski/Kalamazoo Gazette-MLive Media Group via AP, File)

FILE - Rescue workers and residents search through the rubble in the aftermath of a strike on a girls' elementary school in Minab, Iran, Feb. 28, 2026. (Abbas Zakeri/Mehr News Agency via AP, file)
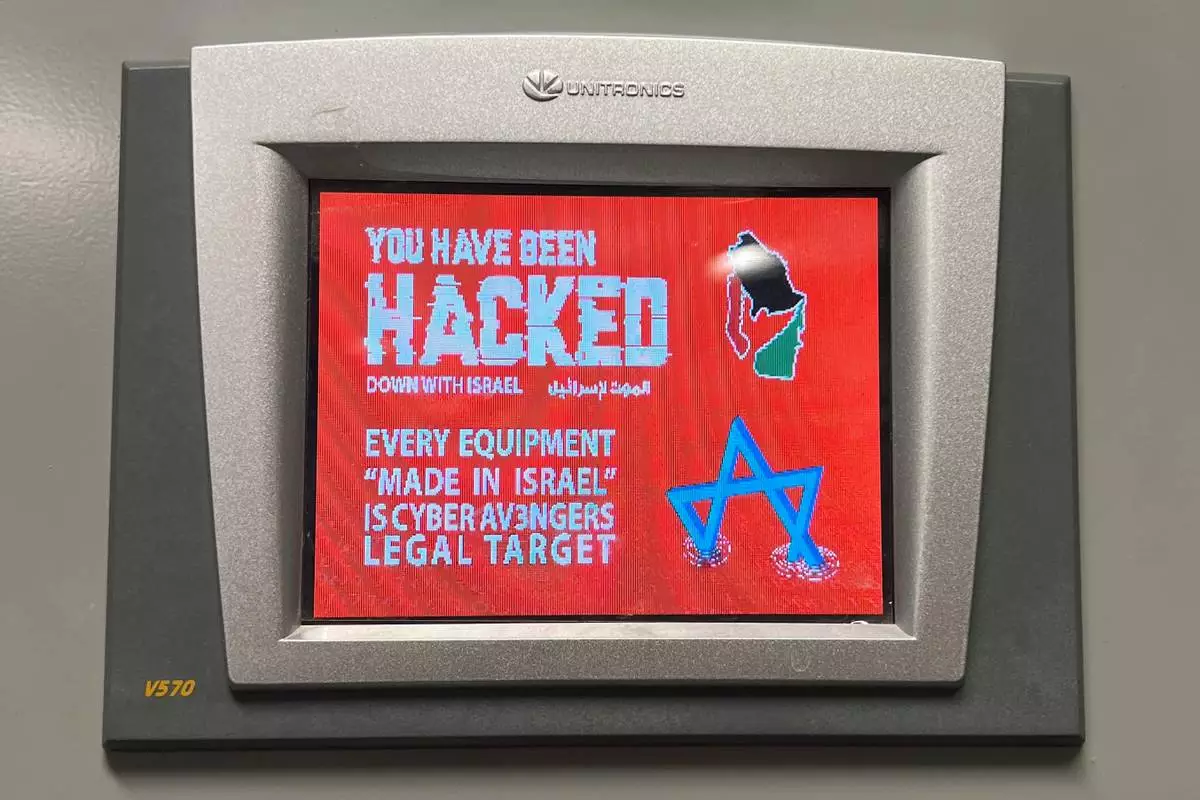
FILE - This photo provided by the Municipal Water Authority of Aliquippa shows the screen of a Unitronics device that was hacked in Aliquippa, Pa., Nov. 25, 2023. (Municipal Water Authority of Aliquippa via AP, File)
FILE - The CEO of FireEye Kevin Mandia gives a tour of the cybersecurity company's unused office space in Reston, Va., March 9, 2021. (AP Photo/Nathan Ellgren, file)
Voters across Maine, Nevada, South Carolina and North Dakota were casting ballots Tuesday in another day of primary elections in America, but much of the political world was focused on Maine’s high-stakes U.S. Senate contest.
The results aren't in question. Neither Republican incumbent Sen. Susan Collins nor Democratic challenger Graham Platner faces serious opposition for their party’s nomination. And yet Tuesday marks an especially significant moment for Platner, the embattled veteran and oyster farmer, who's fighting to rebuild his credibility in a campaign rocked by controversy.
Elsewhere, President Donald Trump’s clout within his party was being tested anew in states like South Carolina and Nevada, where he’s endorsed his favored candidates. Democrats hope to build momentum in Nevada in their broader push to reclaim key governor’s seats.
Here's the latest:
Wilson moved forward despite not securing Trump’s endorsement in a race in which the top contenders vied for the president’s support.
Wilson has served as the state’s attorney general since 2011, taking actions to support Trump’s political and personal moves. In 2024, Wilson traveled to New York to support Trump as he stood trial in a hush money case.
He is the son of longtime U.S. Rep. Joe Wilson.
Evette’s achievement came about a week after securing Trump’s backing.
The Ohio native has for eight years served as lieutenant governor to current Gov. Henry McMaster, who is term-limited and was among Trump’s earliest supporters in his first presidential campaign.
In-person Election Day voting concluded in North Dakota at 9 p.m. ET. Some polls located in Central time closed an hour earlier, at 8 p.m. ET.
Comparable primaries from past elections can offer clues about when to expect the first vote results and how long the vote count might take.
In the 2024 state primary, the AP first reported results at 9 p.m. ET, just as the last polls closed. The last vote update of the night was at 11:56 p.m. ET, with about 99% of total votes counted.
The key Trump ally defeated challengers including businessman Mark Lynch, who said Graham wasn’t conservative enough for the state.
Trump early on endorsed Graham, his political confidant and regular golfing partner, despite their on-again-off-again relationship.
In announcing he would seek a fifth term in the Senate, Graham also secured the state’s leading Republicans, Sen. Tim Scott and Gov. Henry McMaster, to chair his 2026 run.
No Democrat has won a U.S. Senate seat in South Carolina in decades, and Republicans in recent history typically take statewide seats by double-digit margins. When he last ran in 2020, Graham defeated his Democratic opponent, Jaime Harrison, by a 10 percentage point margin.
A number of Republican challengers are vying against Graham, but one voter said he’s not worried about arguments the incumbent isn’t conservative enough.
“I think he’s perfectly fine,” said Jimmy Hunt, a Spartanburg businessman, as he watched returns come in at Lt. Gov. Pamela Evette’s election night headquarters in Greenville.
“He navigates pretty well with President Trump,” Hunt said. He’s kind of always on the edge of being in trouble, but that’s a tough game — really tough.”
The state lawmaker who has represented a district in the Columbia area for three terms defeated businessman Billy Webster and attorney Mullins McLeod.
Seen as a rising star in the state party, Johnson was tapped to give this year’s Democratic response to Republican Gov. Henry McMaster’s state of the state address.
The winner of the November general election will succeed McMaster, who has been in office since Nikki Haley left her term early to join the first Trump administration.
Democrats have not won a general election for governor in South Carolina since 1998, and Republicans have controlled all statewide elected offices for more than a decade.
The Charleston pediatrician secured the nomination in her campaign to keep Republican U.S. Sen. Lindsey Graham from a fifth term.
Andrews, who unsuccessfully challenged U.S. Rep. Nancy Mace in 2022, has challenged what she’s characterized as Graham’s waffling positions over the course of his political career.
No Democrat has won a U.S. Senate seat in South Carolina in decades, and Republicans in recent history typically take statewide seats by double-digit margins.
When he last ran in 2020, Graham defeated his Democratic opponent, Jaime Harrison, by a 10 percentage point margin.
Platner is holding his event at Blue Hill YMCA in the town of Blue Hill, about 30 miles from his hometown of Sullivan. Supporters were gathering to hear a speech from Platner, which is expected after results come in.
Platner is expected to win the primary because his main competition, Democratic Gov. Janet Mills, suspended her campaign weeks ago. The winner will face longtime Republican Sen. Susan Collins.
The mood at his event is high, with the crowd expecting a victory and beginning to assemble in front of a podium where Platner will speak.
Las Vegas resident Laurie Trowbridge voted for Alexis Hill because of Hill’s stance on data centers. Hill has pledged to stop new tax abatements on data centers and require them to implement renewable energy policies.
“We don’t have enough water for data centers,” Trowbridge said. “And they pollute everything, and we can’t have it. We have enough problems in the state without adding that to it.”
Teresa Ray, also a Las Vegas resident, voted for Attorney General Aaron Ford because of his experience as a leader.
“He has shown me since he’s been attorney general that he’s going to be the one that should be able to lead Nevada into a better place than where we are now,” Ray said.
She hopes that if he is elected, he will be able to encourage other Democrats to “grow some spine” and send a better message to voters.
Juliana Palyak studied the Republican candidates for South Carolina governor for months. She didn’t like any of them.
Finally as primary day came, she said she decided to vote for self-funded businessman Rom Reddy.
“I do not want career politicians any more. I am tried of it,” Paylak said of the other four candidates who are all currently in elected office.
Her disgust extends to Trump, who has lost her support by going to war in Iran and not keeping other promises made during his campaign.
“His social media. It’s ridiculous,” Paylak said.
In-person Election Day voting concluded in Maine at 8 p.m. ET.
Comparable primaries from past elections can offer clues about when to expect the first vote results and how long the vote count might take.
In the 2024 general election, the AP first reported results at 8:44 p.m. ET, or 44 minutes after polls closed. About 50% of the total vote had been counted by 12:54 a.m. ET, and counting stopped for the night at 4:11 a.m. ET. By 3:13 p.m. ET the day after Election Day, about 90% of the vote had been counted.
Some of Maine’s primary elections could advance to ranked choice voting if no candidate wins a majority of first-choice votes. This could delay the release of final results for another week or two.
Hilton has made the case that the state desperately needs new leadership following more than 15 years of Democratic dominance.
He’ll face Democrat Xavier Becerra, a former state attorney general and Biden administration health secretary, whom The Associated Press previously determined had won enough votes. Election day was a week ago.
Hilton faces a challenging electorate in the November election, as California has nearly twice as many registered Democrats as Republicans. If elected he would be the first GOP candidate to win statewide office since 2006.
Gov. Joe Lombardo thanked campaign volunteers Tuesday afternoon in front of a Las Vegas polling location, taking pictures and signing supporters’ shirts as people huddled under a tent in the 94 degree heat.
The Republican governor, who is expected to easily win his primary, touted his record on improving education and “expanding upon the economy and the jobs front, healthcare, and public safety.” He said next on the list is working on affordable housing.
“We’re running again because we still got a lot of work to do in that space,” Lombardo said at his campaign’s booth. Along the sidewalk leading to the polling location, campaigns sent up booths in a last effort to sway voters.
Lombardo will likely face either Attorney General Aaron Ford or Washoe County Commissioner Alexis Hill in November.
Election day in California was one week ago, but candidates in the race for governor are still waiting to find out who will be paired in a November runoff for the state’s highest office.
Democrat Xavier Becerra qualified last week, but it’s still not clear if the second spot will be claimed by Republican Steve Hilton or Democrat Tom Steyer.
Becerra told reporters Tuesday that he was “anxious to find out who … is going to be in there with me.”
California has a notoriously slow vote count, and Becerra said, “I don’t think it’s a great thing that it takes such a long time.” But he also defended the system, saying he would oppose “anything that reduces a Californian’s chance to vote.”
Earlier in the day, Hilton said the vote-counting system that can sometimes take weeks or longer to determine a winner desperately needed a complete overhaul.
“It’s insane,” Hilton said.
Two of the GOP candidates said they felt the use of ranked choice voting in the GOP primary made for an uglier election season.
Maine uses the ranked the style of voting for some races, including governor primaries, though it will not be used in the general election for governor. Ranked voting could factor heavily in Tuesday’s results because there are seven Republican candidates and five Democrats.
Jonathan Bush, one of the Republican candidates, said the role of ranked choice voting is to “make people less trusting of our democracy right now.” Another Republican, Owen McCarthy, said it led to candidates attacking each other.
“The thing with ranked choice voting is it’s supposed to make the race nicer. It didn’t make the race nicer,” he said.
The state’s primaries seemed to be on the verge of being upended over Trump’s push to reshape congressional districts ahead of the November elections.
However, the Republican-controlled state Senate rejected a plan to cancel congressional votes and schedule a new primary under revised districts.
The new lines had been designed to help Republicans oust U.S. Rep. Jim Clyburn, currently seeking his 18th term and the state’s sole congressional Democrat.
Some senators, including Republicans, said it was simply too late to make a change. Last weekend, South Carolina Democrats celebrated during their annual fundraising dinner and convention.
The Maine Democratic Senate candidate has been scrutinized recently after reports that he sent sexually explicit text messages with several women while married to his wife, Amy Gertner.
Gertner has called news coverage of the issue “gossip.”
Genevieve McDonald, a then-campaign staffer for Platner, told The Associated Press that Platner was “sexting multiple women while married” and “the campaign tried to assess that as an election vulnerability.”
According to The Wall Street Journal, Gertner told the campaign in August about the messages, which she had discovered on Platner’s phone last year. Platner’s campaign team reportedly decided that the texts were private and being handled by the couple, who were married in 2023.
The two are in counseling, Gertner has said, and Platner has his own therapist.
Graham often faces primary challengers, and he’s vying against several on Tuesday. But leading up to this year’s primary, several Republicans bowed out before voting began.
André Bauer, a former South Carolina lieutenant governor nominated as ambassador to Belize in both of Trump’s terms, ended up shuttering his bid after only a month as an announced candidate.
And Paul Dans, a chief architect of Project 2025, bailed on the last day to remove his name from ballots.
Mark Lynch, a Greenville businessman, is still running. On social media, Trump has said Lynch “would be a DISASTER for the Republican Party” if elected.
Maine supporters of Graham Platner said Tuesday that ousting incumbent Republican Sen. Susan Collins was on their mind.
Merrill Poddle of Ellsworth, Maine, said he voted for Platner. He questioned how much Collins actually stands up to President Donald Trump.
“The only time that she’s ever voted against him, what he wants, is when she knew it was gonna pass anyway,” he said. “She always has concerns, but that’s about all she ever has.”
Anne Dickens, also of Ellsworth, said she’s backing Platner as well. She questioned whether Collins had a vision for Maine.
“I think that Susan Collins has had her chance. She’s been too conservative and too much with the Trump view,” she said.
Among the several quirks about Maine, it’s one of just two states that uses ranked choice voting for its statewide elections.
It’s a system, adopted in 2016, that allows Maine voters to rank their lesser choices.
If no candidate wins a majority of first-place votes, then other rounds of tabulation begin without the last-place finisher. That candidate’s votes are reallocated to other candidates based on the second-place choices of their voters. The process continues until one candidate has a majority.
The Senate Democratic primary election isn’t expected to head to ranked choice voting, but other races might, including the one for governor.
Democratic governor candidate Nirav Shah has campaigned asking to be voters’ second choice if he can’t be their first, joking in a recent ad that “second choices are still pretty good … most of the time!”
▶ Read more
No Democrat has held the congressional seat that represents Reno and rural northern Nevada, but Democrats aren’t ruling it out this year after longtime GOP Rep. Mark Amodei announced his retirement.
“A lot of things have to go our way in November, and I think we should be honest about that,” said Erik Jimenez, chair of the Democratic Party of Washoe County, the most populous county in the district. “But I’ll say from our volunteer base in Washoe and just rank-and-file voters across the district, we have never seen more people excited about Congressional District 2 than we do now.”
Former state lawmaker Teresa Benitez-Thompson and businessman and investor Greg Kidd are among those on the Democratic primary ballot. They've focused on the economy, healthcare and artificial intelligence regulations.
Democrats are banking on Trump’s growing unpopularity and the district’s large number of nonpartisan voters. In the Republican primary, they're hoping that Trump-backed candidate David Flippo will defeat James Settelmeyer, a former lawmaker with the backing of Gov. Joe Lombardo, believing it would be easier to draw a contrast.
North Dakota’s lone U.S. House member faces a partial rematch of her 2024 nomination race in a state primary Tuesday. Also on the ballot is a proposed amendment to the state constitution, while residents of Fargo will elect a new mayor.
Republican U.S. Rep. Julie Fedorchak seeks a second term. She faces another primary challenge from former foreign service officer Alex Balazs, who placed fourth in the 2024 contest with 4% of the vote behind her and others. Fedorchak went on to win the general election with 69% of the vote against Democrat Trygve Hammer, who also is running again and will face the winner of this year’s Republican primary.
Voters will also choose nominees for several top statewide offices, although candidates for most of those offices, such as secretary of state, state attorney general and state agriculture commissioner, are running unopposed.
Many of the state’s top elected offices, such governor, lieutenant governor, treasurer and both U.S. Senate seats, won’t be up for election until 2028 or later.
▶ Read more
More than a year before filing even opened for this year’s contests, Graham’s campaign said Sen. Tim Scott and Gov. Henry McMaster would chair his 2026 run.
Scott, South Carolina’s junior senator, chairs the National Republican Senatorial Committee.
McMaster is the state’s longest-serving governor, having been elected twice after serving the remaining two years of Nikki Haley’s term after she became Trump’s first ambassador to the United Nations.
Democrats and Republicans will pick nominees for governor to replace Mills as the Democrat’s time in office is winding to a close.
It’s a crowded field. Democrats are choosing between Maine Secretary of State Shenna Bellows; former Maine Senate President Troy Jackson; former Speaker of the Maine House of Representatives Hannah Pingree; energy executive Angus King III; and former director of the Maine Center for Disease Control and Prevention Nirav Shah.
Republicans will choose between former U.S. Assistant Secretary of State Bobby Charles; healthcare executive Jonathan Bush; former Maine Senate Majority Leader Garrett Mason; University of Maine System trustee Owen McCarthy; former Paris, Maine, selectman Robert Wessels; and businessmen David Jones and Ben Midgley.
Mills is termed out and will appear on the Democratic ballot for U.S. Senate, although she suspended her campaign weeks ago.
As Nevada voters participate in primary elections Tuesday, the state Democratic Party has launched a website — www.thelombardotrumpway.com/ — to highlight GOP Gov. Joe Lombardo’s connections to the White House.
The site is an effort to connect the governor to the economic fallout from Trump’s tariffs and the Iran war. Lombardo is considered one of the most vulnerable governors in the country.
The Democrats vying to challenge Lombardo include state Attorney General Aaron Ford, who has the backing of the Democratic congressional delegation and former Vice President Kamala Harris. He would be the first Black man elected governor of Nevada. He’s facing Democrat Alexis Hill, a county commissioner in northern Nevada who campaigned as a candidate willing to shake things up.
Platner’s campaign has spent months navigating controversies about a tattoo of a Nazi symbol that he had covered up and his history of inflammatory online postings.
Platner has said he was drunk on leave with some fellow Marines many years ago when he got a skull and crossbones tattoo on his chest. He had it covered up last year after saying he learned that it was a Nazi image.
There has also been much attention on his former social media and Reddit posts, which were dismissive of military sexual assaults, insulting of police and rural residents and used homophobic slurs, for which he's apologized.
A person walks past a sign for a drive-through ballot drop-off outside the city hall in Las Vegas, Tuesday, June 9, 2026. (AP Photo/Jae C. Hong)

Lindsay Robinson, with daughter Scottie, walks to cast her ballots in the Maine Primary, Tuesday, June 9, 2026, in Augusta, Maine. (AP Photo/Robert F. Bukaty)

Mary Saunders looks over her choices one last time before casting her ballots in the Maine Primary, Tuesday, June 9, 2026, in Augusta, Maine. (AP Photo/Robert F. Bukaty)