|
In the news release, Bybit Uncovers AI-Assisted macOS Malware Campaign Targeting Users Searching for Claude Code, issued 21-Apr-2026 by Bybit over PR Newswire, we are advised by the company that the headline and 9th paragraph have been updated. The complete, corrected release follows:
AI empowered Bybit Security Team Uncovers macOS Malware Campaign Targeting Users Searching for Claude Code
DUBAI, UAE, April 21, 2026 /PRNewswire/ -- Bybit, the world's second-largest cryptocurrency exchange by trading volume, reported that its Security Operations Center (SOC) disclosed findings detailing a sophisticated, multi-stage malware campaign targeting macOS users searching for "Claude Code," an AI-powered development tool from Anthropic.
The report marks one of the first known disclosures by a centralized crypto exchange (CEX) of an active threat campaign targeting developers via AI tool discovery channels, underscoring the sector's growing role in frontline cybersecurity intelligence.
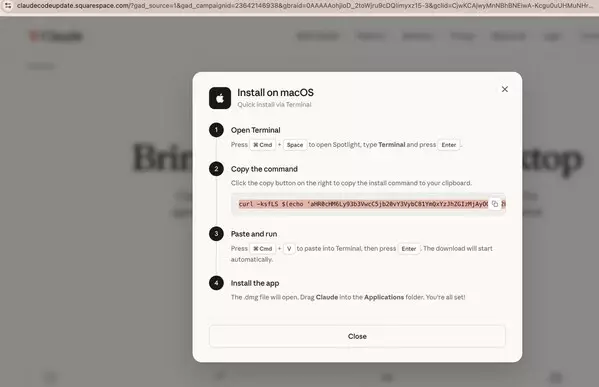
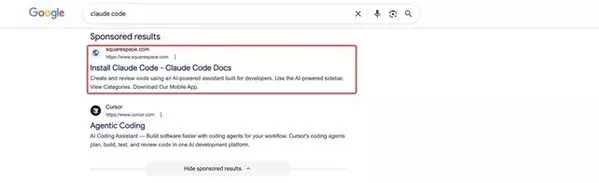
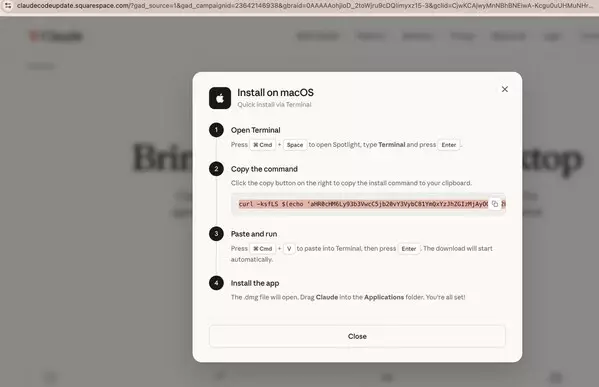
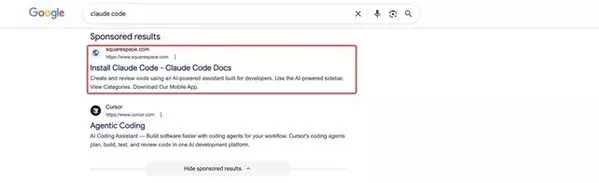
First identified in March 2026, the campaign used search engine optimization (SEO) poisoning to elevate a malicious domain to the top of Google search results. Users were redirected to a spoofed installation page designed to closely resemble legitimate documentation, triggering a two-stage attack chain focused on credential harvesting, crypto asset targeting, and persistent system access.
The initial payload, delivered via a Mach-O dropper, deployed an osascript-based infostealer exhibiting characteristics similar to known AMOS and Banshee variants. It executed a multi-phase obfuscation sequence to extract sensitive data including browser credentials, macOS Keychain entries, Telegram sessions, VPN profiles, and cryptocurrency wallet information. Bybit researchers identified targeted access attempts against more than 250 browser-based wallet extensions and multiple desktop wallet applications.
A second-stage payload introduced a C++-based backdoor with advanced evasion capabilities, including sandbox detection and encrypted runtime configurations. The malware established persistence through system-level agents and enabled remote command execution via HTTP-based polling, granting attackers ongoing control over compromised devices.
Bybit's SOC leveraged AI-assisted workflows across the full malware analysis lifecycle, significantly accelerating response time while maintaining analytical depth. Initial triage and classification of the Mach-O sample were completed within minutes, with models flagging behavioral similarities to known malware families.
AI-assisted reverse engineering and control-flow analysis reduced the time required for deep inspection of the second-stage backdoor from an estimated six to eight hours to under 40 minutes. At the same time, automated extraction pipelines identified indicators of compromise (IOCs) – including command-and-control infrastructure, file signatures, and behavioral patterns – and mapped them to established threat frameworks.
These capabilities enabled same-day deployment of detection measures. AI-assisted rule generation supported the creation of threat signatures and endpoint detection rules, which analysts validated before being pushed into production environments. AI-generated reporting drafts further reduced turnaround time, allowing threat intelligence outputs to be finalized approximately 70% faster than traditional workflows.
"As one of the first crypto exchanges to publicly document this type of malware campaign, we believe sharing these findings is critical to strengthening collective defense across the industry," said David Zong, Head of Group Risk Control and Security at Bybit. "Our AI-assisted SOC allows us to move from detection to full kill chain visibility within a single operational window. What used to require a team of analysts working across multiple shifts – decompilation, IOC extraction, report drafting, rule writing – was completed in a single session with AI handling the heavy lifting and our analysts providing judgment and validation. Looking to the future, we will face an AI war. Using AI to defend against AI is an inevitable trend. Bybit will further increase its investment in AI for security, achieving minute-level threat detection and automated, intelligent emergency response."
The investigation also revealed social engineering tactics, including fake macOS password prompts used to validate and cache user credentials. In some cases, attackers attempted to replace legitimate crypto wallet applications such as Ledger Live and Trezor Suite with trojanized versions hosted on malicious infrastructure.
The malware targeted a wide range of environments, including Chromium-based browsers, Firefox variants, Safari data, Apple Notes, and local file directories commonly used to store sensitive financial or authentication data.
Bybit identified multiple domains and command-and-control endpoints associated with the campaign, all of which have been defanged for public disclosure. Analysis indicates that attackers relied on intermittent HTTP polling rather than persistent connections, making detection more challenging.
The incident reflects a growing trend of attackers targeting developers through manipulated search results, particularly as AI tools gain mainstream adoption. Developers remain high-value targets due to their access to codebases, infrastructure, and financial systems.
Bybit confirmed that malicious infrastructure was identified on March 12, with full analysis, mitigation, and detection measures completed within the same day. Public disclosure followed on March 20, alongside detailed detection guidance.
#Bybit / #CryptoArk / #NewFinancialPlatform
About Bybit
Bybit is the world's second-largest cryptocurrency exchange by trading volume, serving a global community of over 80 million users. Founded in 2018, Bybit is redefining openness in the decentralized world by creating a simpler, open and equal ecosystem for everyone. With a strong focus on Web3, Bybit partners strategically with leading blockchain protocols to provide robust infrastructure and drive on-chain innovation. Renowned for its secure custody, diverse marketplaces, intuitive user experience, and advanced blockchain tools, Bybit bridges the gap between TradFi and DeFi, empowering builders, creators, and enthusiasts to unlock the full potential of Web3. Discover the future of decentralized finance at Bybit.com.
For more details about Bybit, please visit Bybit Press
For media inquiries, please contact: media@bybit.com
For updates, please follow: Bybit's Communities and Social Media
Discord | Facebook | Instagram | LinkedIn | Reddit | Telegram | TikTok | X | Youtube
In the news release, Bybit Uncovers AI-Assisted macOS Malware Campaign Targeting Users Searching for Claude Code, issued 21-Apr-2026 by Bybit over PR Newswire, we are advised by the company that the headline and 9th paragraph have been updated. The complete, corrected release follows:
DUBAI, UAE, April 21, 2026 /PRNewswire/ -- Bybit, the world's second-largest cryptocurrency exchange by trading volume, reported that its Security Operations Center (SOC) disclosed findings detailing a sophisticated, multi-stage malware campaign targeting macOS users searching for "Claude Code," an AI-powered development tool from Anthropic.
The report marks one of the first known disclosures by a centralized crypto exchange (CEX) of an active threat campaign targeting developers via AI tool discovery channels, underscoring the sector's growing role in frontline cybersecurity intelligence.
First identified in March 2026, the campaign used search engine optimization (SEO) poisoning to elevate a malicious domain to the top of Google search results. Users were redirected to a spoofed installation page designed to closely resemble legitimate documentation, triggering a two-stage attack chain focused on credential harvesting, crypto asset targeting, and persistent system access.
The initial payload, delivered via a Mach-O dropper, deployed an osascript-based infostealer exhibiting characteristics similar to known AMOS and Banshee variants. It executed a multi-phase obfuscation sequence to extract sensitive data including browser credentials, macOS Keychain entries, Telegram sessions, VPN profiles, and cryptocurrency wallet information. Bybit researchers identified targeted access attempts against more than 250 browser-based wallet extensions and multiple desktop wallet applications.
A second-stage payload introduced a C++-based backdoor with advanced evasion capabilities, including sandbox detection and encrypted runtime configurations. The malware established persistence through system-level agents and enabled remote command execution via HTTP-based polling, granting attackers ongoing control over compromised devices.
Bybit's SOC leveraged AI-assisted workflows across the full malware analysis lifecycle, significantly accelerating response time while maintaining analytical depth. Initial triage and classification of the Mach-O sample were completed within minutes, with models flagging behavioral similarities to known malware families.
AI-assisted reverse engineering and control-flow analysis reduced the time required for deep inspection of the second-stage backdoor from an estimated six to eight hours to under 40 minutes. At the same time, automated extraction pipelines identified indicators of compromise (IOCs) – including command-and-control infrastructure, file signatures, and behavioral patterns – and mapped them to established threat frameworks.
These capabilities enabled same-day deployment of detection measures. AI-assisted rule generation supported the creation of threat signatures and endpoint detection rules, which analysts validated before being pushed into production environments. AI-generated reporting drafts further reduced turnaround time, allowing threat intelligence outputs to be finalized approximately 70% faster than traditional workflows.
"As one of the first crypto exchanges to publicly document this type of malware campaign, we believe sharing these findings is critical to strengthening collective defense across the industry," said David Zong, Head of Group Risk Control and Security at Bybit. "Our AI-assisted SOC allows us to move from detection to full kill chain visibility within a single operational window. What used to require a team of analysts working across multiple shifts – decompilation, IOC extraction, report drafting, rule writing – was completed in a single session with AI handling the heavy lifting and our analysts providing judgment and validation. Looking to the future, we will face an AI war. Using AI to defend against AI is an inevitable trend. Bybit will further increase its investment in AI for security, achieving minute-level threat detection and automated, intelligent emergency response."
The investigation also revealed social engineering tactics, including fake macOS password prompts used to validate and cache user credentials. In some cases, attackers attempted to replace legitimate crypto wallet applications such as Ledger Live and Trezor Suite with trojanized versions hosted on malicious infrastructure.
The malware targeted a wide range of environments, including Chromium-based browsers, Firefox variants, Safari data, Apple Notes, and local file directories commonly used to store sensitive financial or authentication data.
Bybit identified multiple domains and command-and-control endpoints associated with the campaign, all of which have been defanged for public disclosure. Analysis indicates that attackers relied on intermittent HTTP polling rather than persistent connections, making detection more challenging.
The incident reflects a growing trend of attackers targeting developers through manipulated search results, particularly as AI tools gain mainstream adoption. Developers remain high-value targets due to their access to codebases, infrastructure, and financial systems.
Bybit confirmed that malicious infrastructure was identified on March 12, with full analysis, mitigation, and detection measures completed within the same day. Public disclosure followed on March 20, alongside detailed detection guidance.
#Bybit / #CryptoArk / #NewFinancialPlatform
About Bybit
Bybit is the world's second-largest cryptocurrency exchange by trading volume, serving a global community of over 80 million users. Founded in 2018, Bybit is redefining openness in the decentralized world by creating a simpler, open and equal ecosystem for everyone. With a strong focus on Web3, Bybit partners strategically with leading blockchain protocols to provide robust infrastructure and drive on-chain innovation. Renowned for its secure custody, diverse marketplaces, intuitive user experience, and advanced blockchain tools, Bybit bridges the gap between TradFi and DeFi, empowering builders, creators, and enthusiasts to unlock the full potential of Web3. Discover the future of decentralized finance at Bybit.com.
For more details about Bybit, please visit Bybit Press
For media inquiries, please contact: media@bybit.com
For updates, please follow: Bybit's Communities and Social Media
Discord | Facebook | Instagram | LinkedIn | Reddit | Telegram | TikTok | X | Youtube
** This press release is distributed by PR Newswire through automated distribution system, for which the client assumes full responsibility. **
Bybit Uncovers AI-Assisted macOS Malware Campaign Targeting Users Searching for Claude Code
Bybit Uncovers AI-Assisted macOS Malware Campaign Targeting Users Searching for Claude Code
CHONGQING, China, April 21, 2026 /PRNewswire/ -- The Group sets out Six Major Leaps and five doubling targets, with RMB 600 billion in revenue and 1.5 million overseas sales in its sights for 2030.
Changan Group held its Global Strategy Launch and Global Partner Conference in Chongqing on April 21, 2026, presenting its "1+4+4+5" strategic framework to approximately 700 delegates. The strategy reinforces and advances the Group's Vast Ocean Plan, with a clear ambition: entry into the global automotive top ten and revenue of RMB 600 billion by 2030.
The "1+4+4+5" strategy is built around one vision: to build a world class automotive group with global competitiveness and homegrown core technologies. It is structured around four business pillars, vehicles, components, services, and next generation ecosystem industries, and four transformation priorities: intelligence, green development, globalization, and integration.
Guided by a two step, ten year roadmap, the Group aims to achieve five doublings by 2030 in new energy vehicle (NEV) sales, overseas vehicle sales, total revenue, total profit, and brand value. The 2030 targets include 2.4 million NEV sales, 1.5 million overseas vehicle sales, revenue of RMB 600 billion, placing the Group among the global automotive top 10; and brand value of RMB 200 billion, achieving inclusion among the world's Top 500 Influential Brands.
"Today we are entering a remarkable new era shaped by profound change and unprecedented opportunity. Every transformation creates the conditions for a new generation of world class enterprises. Changan Group will stay committed to co development and shared prosperity, working with our industry partners with one purpose and one direction, side by side as we move forward."
— Zhu Huarong, Chairman, Changan Group
Six Major Leaps
To drive the strategy, Changan has defined Six Major Leaps, each representing a measurable shift with defined milestones.
The Experience Leap marks a shift from single-domain smart driving to full-vehicle intelligence. Powered by SDA Intelligence, it builds a proactive safety matrix while delivering an end-to-end protection system for users.
The Power Leap moves from traditional energy to green and high-efficiency solutions, advancing a diversified technology portfolio across hybrid, battery electric and hydrogen powertrains, striving to achieve peak carbon emissions by 2027, and building a full-lifecycle carbon management system.
The Scale Leap expands growth from a single source to multiple drivers, with parallel plans to double sales in both new energy vehicles and overseas markets while developing globally competitive flagship models
The Ecosystem Leap upgrades Changan from a "large industry, small ecosystem" model to a "large industry, large ecosystem" model, building a coordinated ecosystem spanning users, industry and services.
The System Leap shifts from traditional control-and-operations management to modern global management, with a focus on building world-class capabilities in innovation, talent and management.
The Value Leap marks Changan's full transition toward an intelligent, low-carbon mobility technology company, to deliver all-round gains in economic, industrial, brand and societal value.
Globalization: Three Major Plans
Guided by the "1+4+4+5" strategy, Changan Group is advancing three major plans: the Green Plan for new energy, the Intelligent Plan for smart mobility, and the Vast Ocean Plan for globalization. Together, these initiatives are accelerating the Group's transformation into a leader in intelligent, low carbon mobility technologies.
The Green Plan is progressing steadily, strengthening Changan Group's core NEV technologies and embedding sustainability across product design, manufacturing, and recycling. This approach supports lower carbon emissions across the full vehicle lifecycle. The Intelligent Plan is accelerating execution, delivering ultra safe intelligent mobility solutions for users.
The Vast Ocean Plan is gathering pace as Changan continues to advancing its global market development strategy. Guided by principles of long term development, localization, systemization, and integrated ESG, the Group is moving beyond product exports toward comprehensive brand globalization and industrial globalization.
Foundations
The strategy is built on a strong base. In 2025, Changan Group posted 2.913 million vehicle sales, up 8.5 percent year on year, with NEV sales exceeding 1.1 million units. The Group has ranked first in China's National Enterprise Technology Center evaluation for 14 consecutive years. Its 24,000-strong global R&D team has filed 20,935 patents, 71 percent of them invention patents, and participated in the formulation of 408 standards.
Changan currently sells in 118 countries through 1,124 outlets, with 22 overseas manufacturing bases and combined capacity of 350,000 units. Overseas sales crossed 100,000 units in a single month for the first time in March 2026.
Website: www.globalchangan.com
X (Twitter): @globalchangan
Instagram, Facebook, Youtube and TikTok: @changanautomobile
© 2025 Chongqing Changan Automobile Co., Ltd. All rights reserved.
This information is provided for editorial purposes only. Specifications and availability subject to change without notice.
** This press release is distributed by PR Newswire through automated distribution system, for which the client assumes full responsibility. **

Changan Group Advances Global Strategy with "1+4+4+5" Framework, Targeting RMB 600 Billion in Revenue by 2030

Changan Group Advances Global Strategy with "1+4+4+5" Framework, Targeting RMB 600 Billion in Revenue by 2030