|
Arasan announces the industry's first ASIL-D Certification for its CAN XL IP. The certification also covers Arasan's CAN FD IP and CAN 2.0 IP.
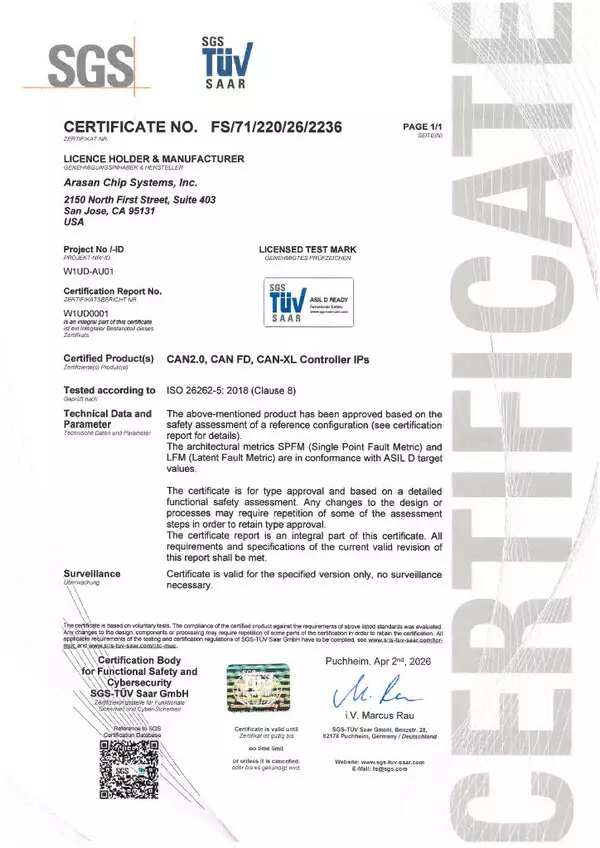
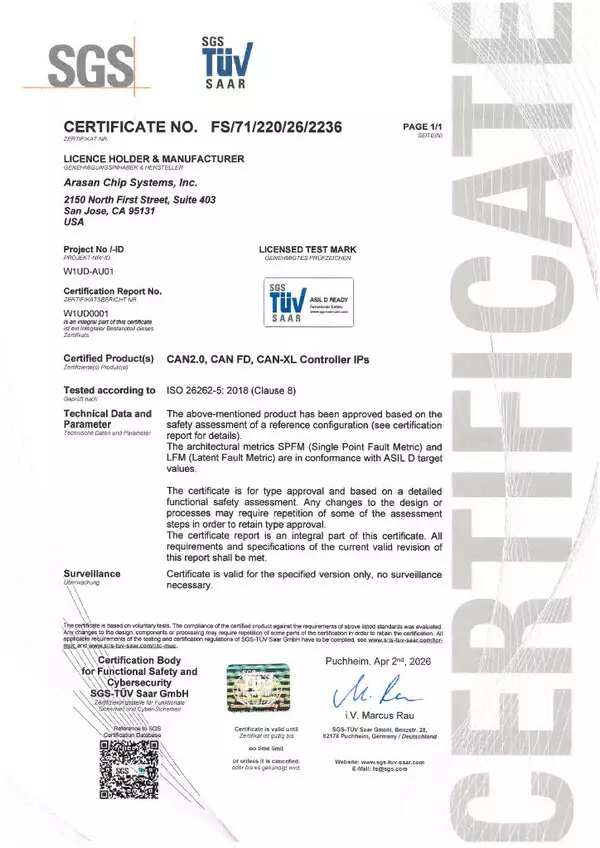
SAN JOSE, Calif., Apr. 21, 2026 /PRNewswire/ -- Arasan Chip Systems, the industry's leading provider of IP for Mobile and Automobile SoC's, announced today that its CAN XL IP has achieved the ASIL-D Certification. The CAN XL IP has been independently certified by SGS-TÜV Saar as ASIL-D, the highest safety level of functional safety defined in ISO 26262, the international standard for functional safety in road vehicles.
The CAN XL IP is backward compatible with the CAN FD and CAN 2.0 standards. The ASIL-D certification also covers Arasan's CAN FD IP and CAN 2.0 IP which will continue to be sold as ASIL-D certified independent products.
Arasan is offering a free upgrade to its CAN XL IP for customers interested in licensing CAN FD until June 30, 2026. The gate count increase from CAN FD to CAN XL is minimal and customers are encouraged to leverage this promotion to adopt the latest version of the CAN Specification, CAN XL.
"Arasan's IP have been used extensively in mission critical and life endangering applications in defense, nuclear, aerospace, medical and automotive ADAS SoC's " said Ron Mabry, VP of Sales at Arasan. "The ASIL-D Certification attests to our fail safe design philosophy".
Arasan's has an extensive portfolio of ASIL-B, ASIL-C and ASIL-D certified products including the MIPI DSI-2 IP for Display, MIPI CSI-2 IP for Camera both of which are seamlessly integrated with the MIPI D-PHY IP or the MIPI C-PHY IP, JEDEC eMMC IP for storage and UNH Certified automotive grade Ethernet IP when high speed automotive connectivity is required.
For more information, please visit: https://www.arasan.com/product/can-bus-controller-ip/
Availability
ASIL-D certified CAN IP products, including the CAN XL IP, CAN FD IP and CAN 2.0 IP, are available to license immediately from Arasan. Please contact sales@arasan.com to license our CAN IP.
Arasan Chip Systems, founded in 1995 is a provider of IP solutions for mobile storage and connectivity interfaces. Arasan's focus lies in mobile SoCs, which have evolved to encompass a wide range of applications, from PDAs in the mid-'90s to today's automobiles, drones, and IoT devices. Arasan remains at the forefront of this "Mobile" evolution, providing standards-based IP that forms the foundation of Mobile SoCs. Over a billion chips have been shipped with Arasan's IP.
Arasan announces the industry's first ASIL-D Certification for its CAN XL IP. The certification also covers Arasan's CAN FD IP and CAN 2.0 IP.
SAN JOSE, Calif., Apr. 21, 2026 /PRNewswire/ -- Arasan Chip Systems, the industry's leading provider of IP for Mobile and Automobile SoC's, announced today that its CAN XL IP has achieved the ASIL-D Certification. The CAN XL IP has been independently certified by SGS-TÜV Saar as ASIL-D, the highest safety level of functional safety defined in ISO 26262, the international standard for functional safety in road vehicles.
The CAN XL IP is backward compatible with the CAN FD and CAN 2.0 standards. The ASIL-D certification also covers Arasan's CAN FD IP and CAN 2.0 IP which will continue to be sold as ASIL-D certified independent products.
Arasan is offering a free upgrade to its CAN XL IP for customers interested in licensing CAN FD until June 30, 2026. The gate count increase from CAN FD to CAN XL is minimal and customers are encouraged to leverage this promotion to adopt the latest version of the CAN Specification, CAN XL.
"Arasan's IP have been used extensively in mission critical and life endangering applications in defense, nuclear, aerospace, medical and automotive ADAS SoC's " said Ron Mabry, VP of Sales at Arasan. "The ASIL-D Certification attests to our fail safe design philosophy".
Arasan's has an extensive portfolio of ASIL-B, ASIL-C and ASIL-D certified products including the MIPI DSI-2 IP for Display, MIPI CSI-2 IP for Camera both of which are seamlessly integrated with the MIPI D-PHY IP or the MIPI C-PHY IP, JEDEC eMMC IP for storage and UNH Certified automotive grade Ethernet IP when high speed automotive connectivity is required.
For more information, please visit: https://www.arasan.com/product/can-bus-controller-ip/
Availability
ASIL-D certified CAN IP products, including the CAN XL IP, CAN FD IP and CAN 2.0 IP, are available to license immediately from Arasan. Please contact sales@arasan.com to license our CAN IP.
Arasan Chip Systems, founded in 1995 is a provider of IP solutions for mobile storage and connectivity interfaces. Arasan's focus lies in mobile SoCs, which have evolved to encompass a wide range of applications, from PDAs in the mid-'90s to today's automobiles, drones, and IoT devices. Arasan remains at the forefront of this "Mobile" evolution, providing standards-based IP that forms the foundation of Mobile SoCs. Over a billion chips have been shipped with Arasan's IP.
** This press release is distributed by PR Newswire through automated distribution system, for which the client assumes full responsibility. **
Arasan acheives the Industrys First ASIL-D Certification for its CAN XL IP Core
|
The First Time a Game in the Legendary Franchise Comes to Consoles
BELLEVUE, Wash., June 6, 2026 /PRNewswire/ -- Critically-acclaimed game development studio ArenaNet® tonight announced Guild Wars 3™, the third entry in the legendary and beloved Guild Wars® MMORPG franchise and their first new game since 2012. The game will release globally on PC, Steam, and PlayStation 5, marking the first time a Guild Wars game will appear on home consoles. The first beta test is scheduled for fall of 2027.
The official debut trailer features the first in-engine gameplay footage and can be viewed HERE. The first concept art and other assets are hosted at the Guild Wars 3 official press kit.
"Guild Wars 3 is a new era not just for ArenaNet and Guild Wars, but also for MMORPGs as a whole," said Colin Johanson, Guild Wars 3 Game Director and ArenaNet Studio Head. "The MMORPG genre has millions of players worldwide eager for new, modern experiences, and the opportunity to harness that excitement is immense. Our approach with Guild Wars 3 is to push MMORPGs forward, to create an online game world that feels believable, rewarding, responsive, and innovative while at the same time respecting players' time and providing a positive, supportive space to build community and enjoy new stories in our universe."
Taking place over a thousand years before the events of the original game, Guild Wars 3 is set in the Tyrian region of Orr, a vast wilderness frontier imbued with the world's magic. Nature entities with strong connections to the land called Vael spirits embody the vitality of this lush, verdant landscape. Various guilds are engaged in conflict over how to protect or exploit the bounty beyond civilization's borders. These multitudinous spirits will vary in size and influence within the ecosystems around them, with the most notable of these being the Seeker. As seen in the trailer, every player's Seeker will serve as a connection to the spirits of Orr and a mount that will carry them on their journeys through the game's open world.
Players will assume the role of a Vaelwarden, a member of a guild of adventurers committed to preserving and protecting both the spirits of the wild and the land of Orr itself. Through the deep character customization and skill-building gameplay the Guild Wars franchise is known for, players will seek adventure and confront danger across this sumptuous, vibrant online world, growing their relationships with the spirits of the wild, the inhabitants of Orr, and other Vaelwarden players.
A combat system designed from the outset to feel great on both a controller and keyboard rewards positioning by emphasizing the joy of movement and momentum. As players seamlessly transition between various movement modes, they can harness their speed and turn it into bigger damage and impact when fighting their foes.
More information about pricing, beta tests, release date, and gameplay features will be revealed later in 2026 and into 2027. Guild Wars 3 will be available directly from the developers at GuildWars3.com, and can be wishlisted on Steam and the PlayStation Store beginning today, with more information available at the game's official website.
About the Guild Wars Franchise
Guild Wars is the award-winning, visually stunning MMORPG franchise that originally launched in 2005 on PC. Boasting a timeless art-brought-to-life aesthetic, the epic grandeur of massive role-playing environments, fast-paced action combat, large-scale dynamic events that players tackle together in the open world, team-based competitive player-versus-player battles, and a sprawling fantasy storyline, the series is often proclaimed as having the friendliest player community in gaming. Guild Wars was relaunched as Guild Wars Reforged in 2025 and expanded to mobile devices in 2026. Guild Wars 2® launched in 2012 on PC and quickly earned accolades across the industry, including Time Magazine's 2012 Game of the Year. Unlike most competitors, the franchise has always been playable with no subscription fee required, welcoming over 29 million players across its history.
About ArenaNet
ArenaNet is the developer of the best-selling Guild Wars Reforged and the groundbreaking Guild Wars 2 massively multiplayer online PC role-playing games. The studio's mission is to create innovative online worlds, cultivate a vibrant and engaged global community of players, and to incorporate handcrafted artistry into every aspect of their games. ArenaNet formed in 2000, with press and fans consistently calling Guild Wars and Guild Wars 2 two of the best MMOs and RPGs of all time. Based in Bellevue, WA, ArenaNet is a wholly-owned subsidiary of Korean gaming giant NC.
The First Time a Game in the Legendary Franchise Comes to Consoles
BELLEVUE, Wash., June 6, 2026 /PRNewswire/ -- Critically-acclaimed game development studio ArenaNet® tonight announced Guild Wars 3™, the third entry in the legendary and beloved Guild Wars® MMORPG franchise and their first new game since 2012. The game will release globally on PC, Steam, and PlayStation 5, marking the first time a Guild Wars game will appear on home consoles. The first beta test is scheduled for fall of 2027.
The official debut trailer features the first in-engine gameplay footage and can be viewed HERE. The first concept art and other assets are hosted at the Guild Wars 3 official press kit.
"Guild Wars 3 is a new era not just for ArenaNet and Guild Wars, but also for MMORPGs as a whole," said Colin Johanson, Guild Wars 3 Game Director and ArenaNet Studio Head. "The MMORPG genre has millions of players worldwide eager for new, modern experiences, and the opportunity to harness that excitement is immense. Our approach with Guild Wars 3 is to push MMORPGs forward, to create an online game world that feels believable, rewarding, responsive, and innovative while at the same time respecting players' time and providing a positive, supportive space to build community and enjoy new stories in our universe."
Taking place over a thousand years before the events of the original game, Guild Wars 3 is set in the Tyrian region of Orr, a vast wilderness frontier imbued with the world's magic. Nature entities with strong connections to the land called Vael spirits embody the vitality of this lush, verdant landscape. Various guilds are engaged in conflict over how to protect or exploit the bounty beyond civilization's borders. These multitudinous spirits will vary in size and influence within the ecosystems around them, with the most notable of these being the Seeker. As seen in the trailer, every player's Seeker will serve as a connection to the spirits of Orr and a mount that will carry them on their journeys through the game's open world.
Players will assume the role of a Vaelwarden, a member of a guild of adventurers committed to preserving and protecting both the spirits of the wild and the land of Orr itself. Through the deep character customization and skill-building gameplay the Guild Wars franchise is known for, players will seek adventure and confront danger across this sumptuous, vibrant online world, growing their relationships with the spirits of the wild, the inhabitants of Orr, and other Vaelwarden players.
A combat system designed from the outset to feel great on both a controller and keyboard rewards positioning by emphasizing the joy of movement and momentum. As players seamlessly transition between various movement modes, they can harness their speed and turn it into bigger damage and impact when fighting their foes.
More information about pricing, beta tests, release date, and gameplay features will be revealed later in 2026 and into 2027. Guild Wars 3 will be available directly from the developers at GuildWars3.com, and can be wishlisted on Steam and the PlayStation Store beginning today, with more information available at the game's official website.
About the Guild Wars Franchise
Guild Wars is the award-winning, visually stunning MMORPG franchise that originally launched in 2005 on PC. Boasting a timeless art-brought-to-life aesthetic, the epic grandeur of massive role-playing environments, fast-paced action combat, large-scale dynamic events that players tackle together in the open world, team-based competitive player-versus-player battles, and a sprawling fantasy storyline, the series is often proclaimed as having the friendliest player community in gaming. Guild Wars was relaunched as Guild Wars Reforged in 2025 and expanded to mobile devices in 2026. Guild Wars 2® launched in 2012 on PC and quickly earned accolades across the industry, including Time Magazine's 2012 Game of the Year. Unlike most competitors, the franchise has always been playable with no subscription fee required, welcoming over 29 million players across its history.
About ArenaNet
ArenaNet is the developer of the best-selling Guild Wars Reforged and the groundbreaking Guild Wars 2 massively multiplayer online PC role-playing games. The studio's mission is to create innovative online worlds, cultivate a vibrant and engaged global community of players, and to incorporate handcrafted artistry into every aspect of their games. ArenaNet formed in 2000, with press and fans consistently calling Guild Wars and Guild Wars 2 two of the best MMOs and RPGs of all time. Based in Bellevue, WA, ArenaNet is a wholly-owned subsidiary of Korean gaming giant NC.
** This press release is distributed by PR Newswire through automated distribution system, for which the client assumes full responsibility. **

Guild Wars 3, Modern Evolution of the MMORPG, Announced at Summer Game Fest for PC and PlayStation 5